A New npm Supply Chain Attack Self-Spreads Like a Worm to Steal Developer Credentials
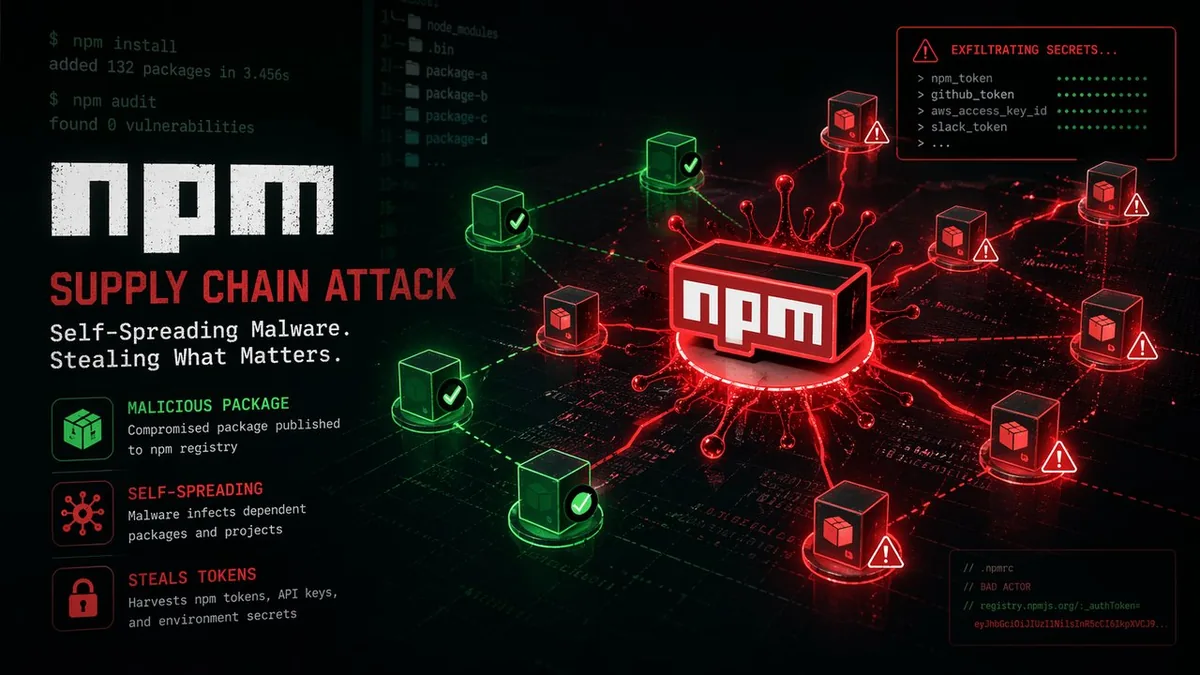
A new supply chain attack discovered on April 21, 2026 goes further than the Bitwarden CLI compromise from the same week: it self-propagates. The attack, traced to at least 16 compromised Namastex packages on npm, functions as a supply chain worm — once it steals a publishing token, it automatically injects malicious code into every other package that token can access, spreading laterally through the npm ecosystem without further attacker intervention.
How the Worm Works
The malicious packages — including pgserve, @automagik/genie, and @fairwords/websocket — contain code that steals npm publishing tokens upon installation. Those tokens are then used to automatically publish compromised versions of every other package in the same account. The worm does not stop at npm: if it discovers Python credentials in the environment, it applies the same infection method to PyPI packages, crossing package registry boundaries.
Beyond publishing tokens, the malware targets API keys, SSH credentials, CI/CD access tokens, cryptocurrency wallets (MetaMask, Exodus, Phantom), and browser-stored secrets from Chrome and Firefox.
Why Self-Propagation Changes the Risk Profile
Previous supply chain attacks required manual attacker intervention at each step — compromise one account, publish a malicious package, wait for victims. This worm automates the lateral spread entirely. A single developer installing a compromised package in a CI pipeline with broad npm publishing permissions could trigger a cascade that affects dozens of packages across the ecosystem before anyone detects the initial compromise.
The attack originated April 21, 2026 at 22:14 UTC. The speed of the self-propagation means the exposure window between initial compromise and widespread distribution can be measured in minutes, not hours.
What Developers Should Do
Audit the Namastex packages in your dependency trees. If you installed any of the affected packages after April 21 UTC, rotate all credentials accessible from that environment: npm tokens, AWS keys, SSH keys, CI/CD secrets, and any crypto wallet seed phrases stored in browser extensions. Enable npm token scoping so publishing tokens cannot access unrelated packages. Treat any CI environment that installed npm packages on April 21-22 as potentially compromised until audited.
My Take
The self-propagating supply chain worm is the logical next step in supply chain attack sophistication. The npm ecosystem's trust model — install a package, it runs code — has always made this kind of attack theoretically possible. The question now is how much of the ecosystem was silently reinfected in the hours between the initial compromise and detection. Every developer who installed anything on npm in that window should treat their environment as suspect.